 All papers examples
All papers examples
Disciplines

- MLA
- APA
- Master's
- Undergraduate
- High School
- PhD
- Harvard
- Biology
- Art
- Drama
- Movies
- Theatre
- Painting
- Music
- Architecture
- Dance
- Design
- History
- American History
- Asian History
- Literature
- Antique Literature
- American Literature
- Asian Literature
- Classic English Literature
- World Literature
- Creative Writing
- English
- Linguistics
- Law
- Criminal Justice
- Legal Issues
- Ethics
- Philosophy
- Religion
- Theology
- Anthropology
- Archaeology
- Economics
- Tourism
- Political Science
- World Affairs
- Psychology
- Sociology
- African-American Studies
- East European Studies
- Latin-American Studies
- Native-American Studies
- West European Studies
- Family and Consumer Science
- Social Issues
- Women and Gender Studies
- Social Work
- Natural Sciences
- Anatomy
- Zoology
- Ecology
- Chemistry
- Pharmacology
- Earth science
- Geography
- Geology
- Astronomy
- Physics
- Agriculture
- Agricultural Studies
- Computer Science
- Internet
- IT Management
- Web Design
- Mathematics
- Business
- Accounting
- Finance
- Investments
- Logistics
- Trade
- Management
- Marketing
- Engineering and Technology
- Engineering
- Technology
- Aeronautics
- Aviation
- Medicine and Health
- Alternative Medicine
- Healthcare
- Nursing
- Nutrition
- Communications and Media
- Advertising
- Communication Strategies
- Journalism
- Public Relations
- Education
- Educational Theories
- Pedagogy
- Teacher's Career
- Statistics
- Chicago/Turabian
- Nature
- Company Analysis
- Sport
- Paintings
- E-commerce
- Holocaust
- Education Theories
- Fashion
- Shakespeare
- Canadian Studies
- Science
- Food Safety
- Relation of Global Warming and Extreme Weather Condition
Paper Types

- Movie Review
- Essay
- Admission Essay
- Annotated Bibliography
- Application Essay
- Article Critique
- Article Review
- Article Writing
- Assessment
- Book Review
- Business Plan
- Business Proposal
- Capstone Project
- Case Study
- Coursework
- Cover Letter
- Creative Essay
- Dissertation
- Dissertation - Abstract
- Dissertation - Conclusion
- Dissertation - Discussion
- Dissertation - Hypothesis
- Dissertation - Introduction
- Dissertation - Literature
- Dissertation - Methodology
- Dissertation - Results
- GCSE Coursework
- Grant Proposal
- Admission Essay
- Annotated Bibliography
- Application Essay
- Article
- Article Critique
- Article Review
- Article Writing
- Assessment
- Book Review
- Business Plan
- Business Proposal
- Capstone Project
- Case Study
- Coursework
- Cover Letter
- Creative Essay
- Dissertation
- Dissertation - Abstract
- Dissertation - Conclusion
- Dissertation - Discussion
- Dissertation - Hypothesis
- Dissertation - Introduction
- Dissertation - Literature
- Dissertation - Methodology
- Dissertation - Results
- Essay
- GCSE Coursework
- Grant Proposal
- Interview
- Lab Report
- Literature Review
- Marketing Plan
- Math Problem
- Movie Analysis
- Movie Review
- Multiple Choice Quiz
- Online Quiz
- Outline
- Personal Statement
- Poem
- Power Point Presentation
- Power Point Presentation With Speaker Notes
- Questionnaire
- Quiz
- Reaction Paper
- Research Paper
- Research Proposal
- Resume
- Speech
- Statistics problem
- SWOT analysis
- Term Paper
- Thesis Paper
- Accounting
- Advertising
- Aeronautics
- African-American Studies
- Agricultural Studies
- Agriculture
- Alternative Medicine
- American History
- American Literature
- Anatomy
- Anthropology
- Antique Literature
- APA
- Archaeology
- Architecture
- Art
- Asian History
- Asian Literature
- Astronomy
- Aviation
- Biology
- Business
- Canadian Studies
- Chemistry
- Chicago/Turabian
- Classic English Literature
- Communication Strategies
- Communications and Media
- Company Analysis
- Computer Science
- Creative Writing
- Criminal Justice
- Dance
- Design
- Drama
- E-commerce
- Earth science
- East European Studies
- Ecology
- Economics
- Education
- Education Theories
- Educational Theories
- Engineering
- Engineering and Technology
- English
- Ethics
- Family and Consumer Science
- Fashion
- Finance
- Food Safety
- Geography
- Geology
- Harvard
- Healthcare
- High School
- History
- Holocaust
- Internet
- Investments
- IT Management
- Journalism
- Latin-American Studies
- Law
- Legal Issues
- Linguistics
- Literature
- Logistics
- Management
- Marketing
- Master's
- Mathematics
- Medicine and Health
- MLA
- Movies
- Music
- Native-American Studies
- Natural Sciences
- Nature
- Nursing
- Nutrition
- Painting
- Paintings
- Pedagogy
- Pharmacology
- PhD
- Philosophy
- Physics
- Political Science
- Psychology
- Public Relations
- Relation of Global Warming and Extreme Weather Condition
- Religion
- Science
- Shakespeare
- Social Issues
- Social Work
- Sociology
- Sport
- Statistics
- Teacher's Career
- Technology
- Theatre
- Theology
- Tourism
- Trade
- Undergraduate
- Web Design
- West European Studies
- Women and Gender Studies
- World Affairs
- World Literature
- Zoology
Network Planning and Implementation, Essay Example
Hire a Writer for Custom Essay
Use 10% Off Discount: "custom10" in 1 Click 👇
You are free to use it as an inspiration or a source for your own work.

Implementing a Network
We have to consider Information technology as a facilitator and automation sector to improve and support business functions effectively. It is vital for the computer network to align network configuration and services according to the business requirements and that may not create a conflict that may ultimately impact on business operations. Static IP address is a configuration of fixed IP address on the workstation. For instance, workstation A and workstation B both share a different IP address in order to communicate via network. Likewise, static IP addressing scheme address some issues that will restrict the workstation to a single subnet. If there is a requirement for connecting the workstation to another subnet, configuration is required. Moreover, this scheme also uses more resources because if the workstation is powered on, broadcasting is active that may consume unnecessary bandwidth and network utilization. Furthermore, if location of the workstation moves from one department to another that is running on different subnet, IP addresses configuration is again required, in order to configure the workstation on the network. There is a requirement for addressing these limitations because in this information age, networks are large and complex and application associated with it also requires flexibility for integration.
In order to cope up with the challenges of configuring IP address again and again, dynamic host configuration protocol (DHCP) served the purpose. DHCP is a simple protocol that is operational on port 67 and 68 of User Datagram Protocol (UDP) (Hunt, 2002). The primary purpose of this protocol is to configure all the TCP/IP settings on the client side without the intervention of human efforts. Under the heading of ‘Requirements for Internet hosts’ mentioned in the RFC also defines that configuration associated with TCP/IP is achievable via DHCP server (Hunt, 2002). Moreover, DHCP assign IP addresses randomly within a specific range or pool of IP addresses defined by the user in the DHCP server configuration. IP lease can also be configured for using the IP address for a limited period of time and after consuming the granted time, IP needs to be leased again or transferred for other services, as it depends on the business requirements (Panek, n.d).
DHCP Installation Guide
For installing a DHCP service or server on the system, configuration is required for defining some parameters and criteria that the service will follow. Windows Server defines a new service as new roles. The configurations steps are mentioned below:
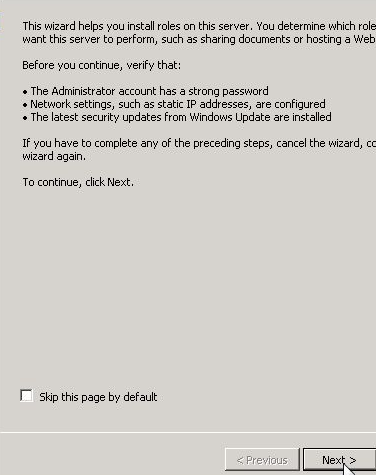
Figure 1.1 (Configuration Wizard)
For configuring DHCP server in Windows 2008 server, this is the first screen that will provide information on defining roles.
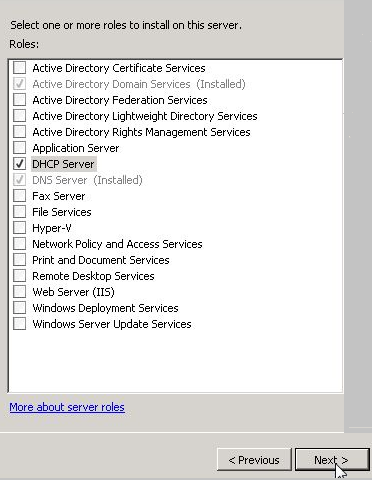
Figure 1.2 (Role Selection)
For installing a DHCP server on the server, DHCP server will be selected, shown in Fig 1.2.
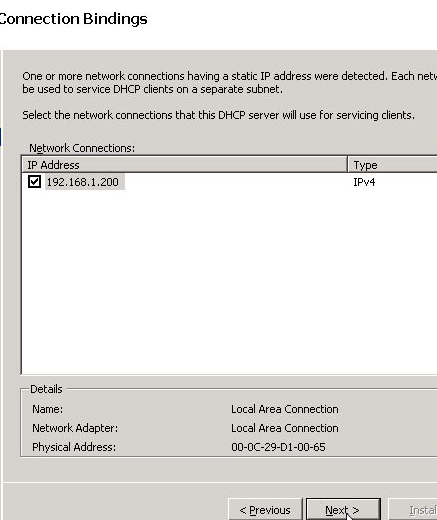
Figure 1.3 (Connection Bindings)
Connection bindings define the type of version and IP address of the DNS server, as shown in Fig 1.3.
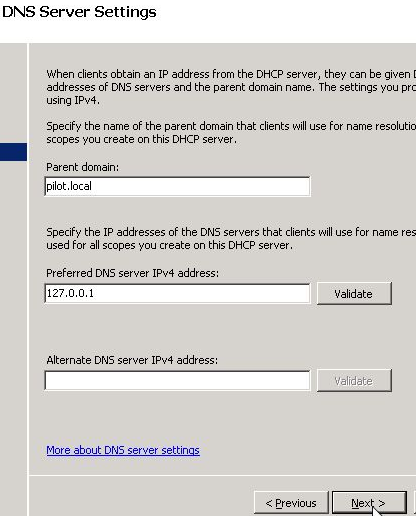
Figure 1.4 (DNS Server Settings)
As shown in Fig 1.4, there is a requirement of defining DNS server settings. Parent domain is usually the domain controller of the organization and the IP address of the system on which the DHCP server will operate. Likewise, if the organization has more than one domain, it will be defined in the ‘Alternate DNS server’ option.
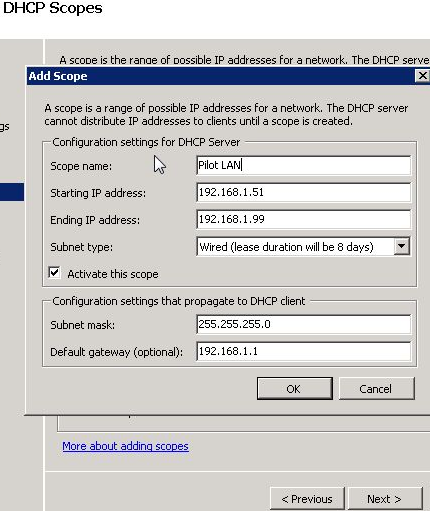
Figure 1.5 (DHCP Scopes)
After defining all the server settings, scope must be defined, as it will assign the IP address to the network by a pool that is mentioned as ‘Starting IP addresses and ‘Ending IP addresses. Name of the scope is Pilot LAN. Moreover, lease duration will also be specified. Furthermore, defining subnets mask and default gateway is required, as DHCP will only lease an IP address to a workstation, if the gateway and subnet mask are same or in range.
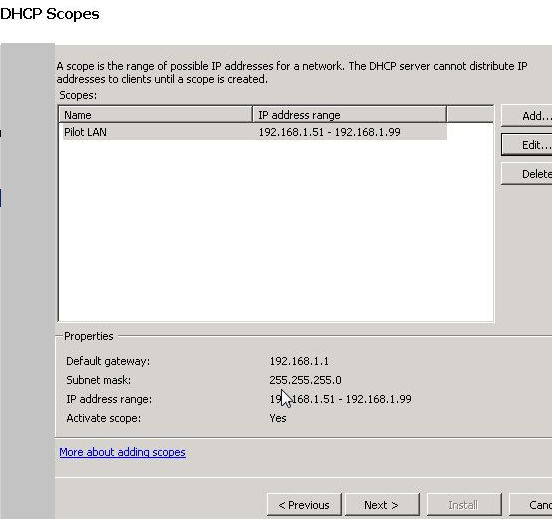
Figure 1.6 (Configured DHCP Scope)
As shown in fig 1.6, DHCP scope is configured. The scope is showing, IP address ranges, Subnet mask, Default gateway, name of the scope, and status of the scope. Moreover, there are more options available to add more scopes.
Figure 1.7 (Installation succeeded)
After configuring and defining the scope of DHCP server, user will click next to finish the installation process, as shown in Fig 1.7.
Networking Tools
IPconfig
As per computer desktop encyclopedia, the command is defined as “A Windows command line utility that is used to manage the IP address assigned to the machine it is running in. Used without any additional parameters, it displays the computer’s currently assigned IP, subnet mask and default gateway addresses. IPCONFIG has several command line switches (parameters); for example, ?ipconfig /all displays a variety of data, including the computer’s name (host name), Ethernet MAC address and DNS server addresses”
Ping
Ping is a small built-in tool that examines the connectivity of the responder i.e. the target host. Likewise, Ping constructs a packet that is send via Internet Control Message Protocol (ICMP) and responds back with the response from the target host. If the host is available or offline, ping command shows information in both cases along with relevant statistics in a shell (Bender,n.d ).
Path Ping
Path ping is another command that combines two commands i.e. Tracert and Ping, to generate required output. Likewise, the command is most suitable in the network environment containing routers or multiple routes between the source and destination of any two workstations or nodes (Morimoto, Noel, & Alex Lewis, n.d ). The output of this command provides statistics related to packet loss on each hop and consequently, faulty or affected router can be identified.
Tracert
This command is named as trace route and it is a UNIX tool, integrated in Microsoft operating systems also. Network engineer can use this command to show the transmission paths of data packets from the network (Tracert.2007).
Netstat
Netstat is named as network statistics and is used as a tool or utility that illustrates the statistics of TCP/IP and Ethernet connections. Network engineers can review metrics and sessions associated with every port that is creating a session or has already established a session (Netstat.2011).
References
Hunt, C. (2002). Linux network servers . San Francisco: SYBEX.
Panek, n.d W.MCTS: Windows server 2008 R2 complete study guide (exams 70-640, 70-642 and 70-643) Sybex.
Ipconfig. (2011). Computer Desktop Encyclopedia, , 1.
Bender, n.d M.MCTS guide to microsoft windows server 2008 network infrastructure configuration (exam #70-642) (networking (course technology)) Course Technology.
Morimoto, R., Noel, M. W., & Alex Lewis, n.d.Microsoft windows server 2003 unleashed (R2 edition) (unleashed) Sams.
Tracert. (2007). Network Dictionary, , 492-492.
Netstat. (2011). Computer Desktop Encyclopedia, , 1-1.

Stuck with your Essay?
Get in touch with one of our experts for instant help!

Time is precious
don’t waste it!
writing help!


Plagiarism-free
guarantee

Privacy
guarantee

Secure
checkout

Money back
guarantee

