 All papers examples
All papers examples
Disciplines

- MLA
- APA
- Master's
- Undergraduate
- High School
- PhD
- Harvard
- Biology
- Art
- Drama
- Movies
- Theatre
- Painting
- Music
- Architecture
- Dance
- Design
- History
- American History
- Asian History
- Literature
- Antique Literature
- American Literature
- Asian Literature
- Classic English Literature
- World Literature
- Creative Writing
- English
- Linguistics
- Law
- Criminal Justice
- Legal Issues
- Ethics
- Philosophy
- Religion
- Theology
- Anthropology
- Archaeology
- Economics
- Tourism
- Political Science
- World Affairs
- Psychology
- Sociology
- African-American Studies
- East European Studies
- Latin-American Studies
- Native-American Studies
- West European Studies
- Family and Consumer Science
- Social Issues
- Women and Gender Studies
- Social Work
- Natural Sciences
- Anatomy
- Zoology
- Ecology
- Chemistry
- Pharmacology
- Earth science
- Geography
- Geology
- Astronomy
- Physics
- Agriculture
- Agricultural Studies
- Computer Science
- Internet
- IT Management
- Web Design
- Mathematics
- Business
- Accounting
- Finance
- Investments
- Logistics
- Trade
- Management
- Marketing
- Engineering and Technology
- Engineering
- Technology
- Aeronautics
- Aviation
- Medicine and Health
- Alternative Medicine
- Healthcare
- Nursing
- Nutrition
- Communications and Media
- Advertising
- Communication Strategies
- Journalism
- Public Relations
- Education
- Educational Theories
- Pedagogy
- Teacher's Career
- Statistics
- Chicago/Turabian
- Nature
- Company Analysis
- Sport
- Paintings
- E-commerce
- Holocaust
- Education Theories
- Fashion
- Shakespeare
- Canadian Studies
- Science
- Food Safety
- Relation of Global Warming and Extreme Weather Condition
Paper Types

- Movie Review
- Essay
- Admission Essay
- Annotated Bibliography
- Application Essay
- Article Critique
- Article Review
- Article Writing
- Assessment
- Book Review
- Business Plan
- Business Proposal
- Capstone Project
- Case Study
- Coursework
- Cover Letter
- Creative Essay
- Dissertation
- Dissertation - Abstract
- Dissertation - Conclusion
- Dissertation - Discussion
- Dissertation - Hypothesis
- Dissertation - Introduction
- Dissertation - Literature
- Dissertation - Methodology
- Dissertation - Results
- GCSE Coursework
- Grant Proposal
- Admission Essay
- Annotated Bibliography
- Application Essay
- Article
- Article Critique
- Article Review
- Article Writing
- Assessment
- Book Review
- Business Plan
- Business Proposal
- Capstone Project
- Case Study
- Coursework
- Cover Letter
- Creative Essay
- Dissertation
- Dissertation - Abstract
- Dissertation - Conclusion
- Dissertation - Discussion
- Dissertation - Hypothesis
- Dissertation - Introduction
- Dissertation - Literature
- Dissertation - Methodology
- Dissertation - Results
- Essay
- GCSE Coursework
- Grant Proposal
- Interview
- Lab Report
- Literature Review
- Marketing Plan
- Math Problem
- Movie Analysis
- Movie Review
- Multiple Choice Quiz
- Online Quiz
- Outline
- Personal Statement
- Poem
- Power Point Presentation
- Power Point Presentation With Speaker Notes
- Questionnaire
- Quiz
- Reaction Paper
- Research Paper
- Research Proposal
- Resume
- Speech
- Statistics problem
- SWOT analysis
- Term Paper
- Thesis Paper
- Accounting
- Advertising
- Aeronautics
- African-American Studies
- Agricultural Studies
- Agriculture
- Alternative Medicine
- American History
- American Literature
- Anatomy
- Anthropology
- Antique Literature
- APA
- Archaeology
- Architecture
- Art
- Asian History
- Asian Literature
- Astronomy
- Aviation
- Biology
- Business
- Canadian Studies
- Chemistry
- Chicago/Turabian
- Classic English Literature
- Communication Strategies
- Communications and Media
- Company Analysis
- Computer Science
- Creative Writing
- Criminal Justice
- Dance
- Design
- Drama
- E-commerce
- Earth science
- East European Studies
- Ecology
- Economics
- Education
- Education Theories
- Educational Theories
- Engineering
- Engineering and Technology
- English
- Ethics
- Family and Consumer Science
- Fashion
- Finance
- Food Safety
- Geography
- Geology
- Harvard
- Healthcare
- High School
- History
- Holocaust
- Internet
- Investments
- IT Management
- Journalism
- Latin-American Studies
- Law
- Legal Issues
- Linguistics
- Literature
- Logistics
- Management
- Marketing
- Master's
- Mathematics
- Medicine and Health
- MLA
- Movies
- Music
- Native-American Studies
- Natural Sciences
- Nature
- Nursing
- Nutrition
- Painting
- Paintings
- Pedagogy
- Pharmacology
- PhD
- Philosophy
- Physics
- Political Science
- Psychology
- Public Relations
- Relation of Global Warming and Extreme Weather Condition
- Religion
- Science
- Shakespeare
- Social Issues
- Social Work
- Sociology
- Sport
- Statistics
- Teacher's Career
- Technology
- Theatre
- Theology
- Tourism
- Trade
- Undergraduate
- Web Design
- West European Studies
- Women and Gender Studies
- World Affairs
- World Literature
- Zoology
The I.T Architecture, Essay Example
Hire a Writer for Custom Essay
Use 10% Off Discount: "custom10" in 1 Click 👇
You are free to use it as an inspiration or a source for your own work.

System Context Diagram for the development of AFS
A system context diagram is a figure used to show the collaboration between peripheral units and the system, it clarifies the boundaries and interface of the system. It has only three symbols. These are a circle, an arrow, and the main process (a box). A circle stands for the system, and the arrow is the slow of data into or from the system. The box is an external entity either human or other systems. It is almost the same with the block diagram. It indicates all the input and output from the system. Its main objective is to concentrate on the external entities and measures that ought to be taken to come up with an absolute system needs and constraints.
In addition, a framework illustration may serve to explicitly, and hurriedly define a project’s scope. Context diagram includes requirements constraints. The framework figure is a subsection of a data flow chart with the framework diagrams being the simplest arrangement of data flow diagrams. It is detailed as it indicates all the processes and data flow.
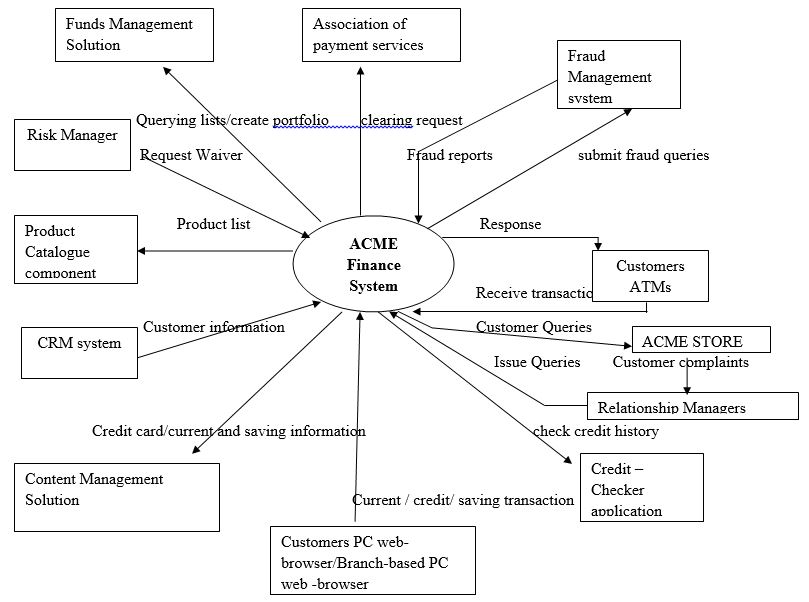
ACME PLC
The Key skills that make IT architect successful
This is the capability of the structure to perform its required task at a period. Availability is the key skills that make an IT Architect successful. This is the concept in which the customer can relate directly with the end user. This is measured in system’s readiness of use and expressed as the availability ratio. The availability of a system ensures the system is ready to do the job required, and provide the need results with the set time. This is very important in that the user will relate directly with the system and will require results. The other skill is performance; this is the point to which a system or element accomplishes its chosen purposes within the stipulated constrains. These include speed, memory usage, or accuracy. It considers the time by which the system takes to responses and its predictability to produce real time results. The system should be able to attain the set up standard and ensure the results are as per the set high standard. The speed to attain these results should also be up to the point. Security is also a very valuable skill of IT architecture.
Security in architecture shows how to position the security countermeasures, and how they interrelate with the overall IT architecture. Security ensures the maintenance of system quality attributes integrity, assurance, and confidentiality. The system should be able to detect intrusion and have a preventive mechanism and should be able to notify the required authority of the insecurity occurred. Maintainability is the aspect in which the system can cope with the changing environment. This is met by making sure that the system can isolate defects and their causes and for it to be able to correct the defects and its causes. The system should also be able to meet the new set of requirements. Maintainability can be either corrective or preventive. Preventive Maintenance refers to the actions required to maintain a system at a specified level of performance. It should be able to trim down the amount of corrective and preventive maintenance needed.
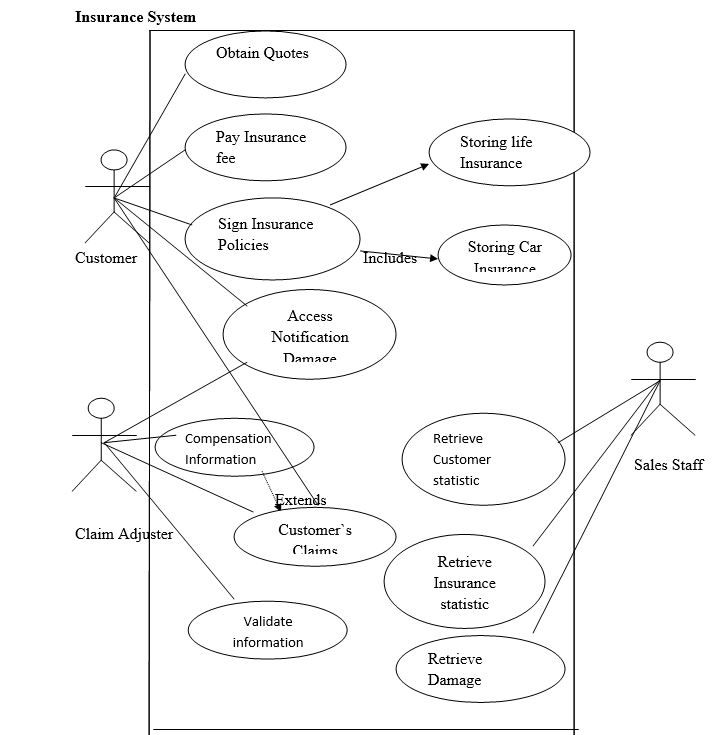
Use Case Diagram
A use case diagram is an illustration use to describe the relationship between the user (actor) and the system or other users in order to attain a given goal. The structure of the use case diagram is the title, primary actor, scope, and level. The use case will interact between the actor and the system. The actor has to be able to make decisions but is not necessarily to be a human being. It is a basic diagram. Use Case diagram for the web-based insurance system.
Insurance System
Availability of an e-commerce system
Modelling availability of Components in Serial
Assumptions:
- I have assumed that since Database server is 100%, I will not use it to calculate the availability.
Availability (A) = A1 x A2 x A3
Application Server (AS) =80%———-A1
Product Catalogue (PC) =90%———–A2
Web server (WS) =40%———–A3
Availability= (80%)*(90%)*(40%)
Availability= 0.8*0.9*0.4= 0.288
Availability for components in serial= 28.8%
Components connected are a chain, relying on the previous component for availability.
The total availability is always lower than the availability of the weakest link
Modelling availability of components in parallel
Availability = 1-[(1-A (1)) x (1- A (2)) x (1-A (3))]
A= 1-[(1-(80%)) x (1-(90%)) x (1-(40%))]
A= 1-[0.2 x 0.1 x 0.6)
A=98.8 %
Component redundancy through duplication
Total availability is higher than the availability of the individual links
Examples for Availability for individual links are;
Application Server (A) = (1-A (1))
=1-80%
=20%
Product Catalogue (A) = (1-A (1))
=1-90%
=10%
Database Manager (A) = (1-A (1))
=1-100%
=0%
Web server (A) = (1-A (1))
=1-40%
=60%

Stuck with your Essay?
Get in touch with one of our experts for instant help!

Time is precious
don’t waste it!
writing help!


Plagiarism-free
guarantee

Privacy
guarantee

Secure
checkout

Money back
guarantee

